
Version: 3.2
2021-04-15
National Information Assurance Partnership

| Version | Date | Comment |
|---|---|---|
| 1.0 | 2013-10-21 | Initial Release |
| 1.1 | 2014-01-12 | Typographical changes and additional clarifications in application notes. Removed assignment from FCS_TLS_EXT.1 and limited testing to those ciphersuites in both FCS_TLS_EXT.1 and FCS_TLS_EXT.2. |
| 2.0 | 2015-09-14 | Included changes based on Technical Rapid Response Team Decisions. Clarified many
requirements and assurance activities. Mandated objective requirements:
Included hardware-isolated REK and key storage selections. Allowed key derivation by REK. Clarified FTP_ITC_EXT.1 and added FDP_UPC_EXT.1. Mandated HTTPS and TLS for application use. (FDP_UPC_EXT.1) Removed Dual_EC_DRBG as an approved DRBG. Adopted new TLS requirements. Mandated TSF Wipe upon authentication failure limit and required number of authentication failures be maintained across reboot. Clarified Management Class. Included more domain isolation discussion and tests. Updated Audit requirements and added Auditable Events table. Added SFR Category Mapping Table. Updated Use Case Templates. Moved Glossary to Introduction. |
| 3.0 | 2015-09-17 | Included changes based on Technical Rapid Response Team Decisions. Clarified many requirements and assurance activities. Mandated objective requirements:
Added SFRs to support BYOD Use Case BYOD Use Case Updated key destruction SFR |
| 3.1 | 2017-04-05 | Included changes based on Technical Rapid Response Team Decisions and incorporated
Technical Decisions. Modified biometric requirements:
FCS_STG_EXT.2.2 - Modified to require long term trusted channel key material be encrypted by an approved method. FIA_UAU_EXT.1.1 - Modified to allow the long term trusted channel key material to be available prior to password being entered at start-up. |
| 3.2 | 2021-04-15 | Removed TLS SFRs and utilized TLS Functional Package Removed Bluetooth SFRs and utilized Bluetooth Module. Bluetooth SFR moved to Implementation Dependent. FPT_TUD_EXT.2.4 renumbered to FPT_TUD_EXT.3.1. FPT_TUD_EXT.3 renumbered to FPT_TUD_EXT.4. FPT_TUD_EXT.4.1 renumbered to FPT_TUD_EXT.5.1. FPT_TUD_EXT.4.2 renumbered to FPT_TUD_EXT.6.1. |
Assurance | Grounds for confidence that a TOE meets the SFRs [CC]. |
Base Protection Profile (Base-PP) | Protection Profile used as a basis to build a PP-Configuration. |
Collaborative Protection Profile (cPP) | A Protection Profile developed by international technical communities and approved by multiple schemes. |
Common Criteria (CC) | Common Criteria for Information Technology Security Evaluation (International Standard ISO/IEC 15408). |
Common Criteria Testing Laboratory | Within the context of the Common Criteria Evaluation and Validation Scheme (CCEVS), an IT security evaluation facility accredited by the National Voluntary Laboratory Accreditation Program (NVLAP) and approved by the NIAP Validation Body to conduct Common Criteria-based evaluations. |
Common Evaluation Methodology (CEM) | Common Evaluation Methodology for Information Technology Security Evaluation. |
Distributed TOE | A TOE composed of multiple components operating as a logical whole. |
Extended Package (EP) | A deprecated document form for collecting SFRs that implement a particular protocol, technology, or functionality. See Functional Packages. |
Functional Package (FP) | A document that collects SFRs for a particular protocol, technology, or functionality. |
Operational Environment (OE) | Hardware and software that are outside the TOE boundary that support the TOE functionality and security policy. |
Protection Profile (PP) | An implementation-independent set of security requirements for a category of products. |
Protection Profile Configuration (PP-Configuration) | A comprehensive set of security requirements for a product type that consists of at least one Base-PP and at least one PP-Module. |
Protection Profile Module (PP-Module) | An implementation-independent statement of security needs for a TOE type complementary to one or more Base-PPs. |
Security Assurance Requirement (SAR) | A requirement to assure the security of the TOE. |
Security Functional Requirement (SFR) | A requirement for security enforcement by the TOE. |
Security Target (ST) | A set of implementation-dependent security requirements for a specific product. |
Target of Evaluation (TOE) | The product under evaluation. |
| The security functionality of the product under evaluation. | |
| A description of how a TOE satisfies the SFRs in an ST. |
Adaptive Template | A type of authentication template that evolves with each sample that is verified and introduced into the biometrics database or gallery. |
Address Space Layout Randomization (ASLR) | An anti-exploitation feature, which loads memory mappings into unpredictable locations. ASLR makes it more difficult for an attacker to redirect control to code that they have introduced into the address space of a process or the kernel. |
Administrator | The Administrator is responsible for management activities, including setting the policy that is applied by the enterprise on the Mobile Device. This administrator is likely to be acting remotely and could be the Mobile Device Management (MDM) Administrator acting through an MDM Agent. If the device is unenrolled, the user is the administrator. |
Authentication Template | A digital representation of an individual’s distinct characteristics, representing information extracted from a biometric sample. Such templates are used during biometric authentication and verification as the basis for comparison. Unlike enrollment templates, these templates can be adaptive. |
Auxiliary Boot Modes | Auxiliary boot modes are states in which the device provides power to one or more components to provide an interface that enables an unauthenticated user to interact with either a specific component or several components that exist outside of the device’s fully authenticated, operational state. |
Biometric Authentication Factor (BAF) | Authentication factor, which uses biometric sample, matched to a biometric authentication template to help establish identity. |
Biometric Data | Digital data created during a biometric process. It encompasses raw sensor observations, biometric samples, models, templates, and/or similarity scores, among other data. This data is used to describe the information collected during an enrollment, verification, or identification process, but does not apply to end user information such as user name, password (unless tied to the biometric modality), demographic information, and authorizations. |
Biometric Sample | Information or computer data obtained from a biometric sensor device or captured from an individual to the sensor. |
Biometric System | Multiple individual components (such as sensor, matching
algorithm, and result display) that combine to make a fully operational system completely
contained within the TOE. A biometric system is automated and capable of:
|
Common Application Developer | Application developers (or software companies) often produce many applications under the same name. Mobile devices often allow shared resources by such applications where otherwise resources would not be shared. |
Critical Security Parameter (CSP) | Security-related information whose disclosure or modification can compromise the security of a cryptographic module and/or authentication system. |
Data | Program/application or data files that are stored or transmitted by a server or Mobile Device (MD). |
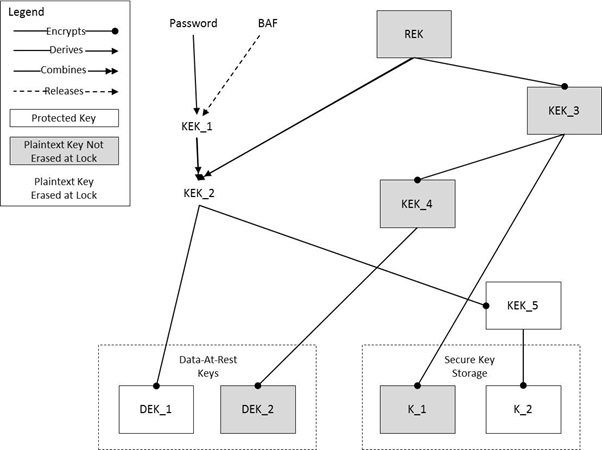
Data Encryption Key (DEK) | A key used to encrypt data-at-rest. |
Developer Modes | Developer modes are states in which additional services are available to a user in order to provide enhanced system access for debugging of software. |
Encrypted Software Keys | These keys are stored in the main file system encrypted by another key and can be changed and sanitized. |
Enrolled State | The state in which the Mobile Device is managed with active policy settings from the administrator. |
Enrollment (Biometrics) | The process of collecting a biometric sample from an end user, converting it into an enrollment and/or authentication template, and storing it in the biometric system’s database. If an enrollment template is generated, it is used during the enrollment process for later comparison to other enrollment templates already stored. If there are multiple enrollment templates, they may be fused, averaged, or otherwise, in order to create authentication templates, which are used for later comparison in verification. |
Enrollment Template | A digital representation of an individual’s distinct characteristics, representing information extracted from a biometric sample. Such templates are generated during the enrollment process and utilized in various ways (including averaging, fusion, etc.) in order to generate an authentication template. |
Enterprise Applications | Applications that are provided and managed by the enterprise. |
Enterprise Data | Enterprise data is any data residing in the enterprise servers, or temporarily stored on Mobile Devices to which the Mobile Device user is allowed access according to security policy defined by the enterprise and implemented by the administrator. |
Ephemeral Keys | These keys are stored in volatile memory. |
False Accept Rate (FAR) | A statistic used to measure biometric performance when operating in verification, defined as the percentage of times a system produces a false accept, which occurs when an individual is incorrectly matched to another individual’s existing biometric. For example, Mallory claims to be Alice and the system verifies the claim. |
False Reject Rate (FRR) | A statistic used to measure biometric performance in verification, defined as the percentage of times the system produces a false reject. A false reject occurs when an individual is not matched to his or her own existing biometric template. For example, John claims to be John, but the system incorrectly denies the claim. |
Feature(s) (Biometrics) | Distinctive mathematical characteristic(s) derived from a biometric sample, used to generate enrollment or authentication templates. |
File Encryption Key (FEK) | A DEK used to encrypt a file or a director when File Encryption is used. FEKs are unique to each encrypted file or directory. |
Hardware-Isolated Keys | The OS can only access these keys by reference, if at all, during runtime. |
Hybrid Authentication | A hybrid authentication factor is one where a user has to submit a combination of a biometric sample and a PIN or password and both to pass. If either factor fails, the entire attempt fails. The user shall not be made aware of which factor failed, if either fails. |
Immutable Hardware Key | These keys are stored as hardware-protected raw key and cannot be changed or sanitized. |
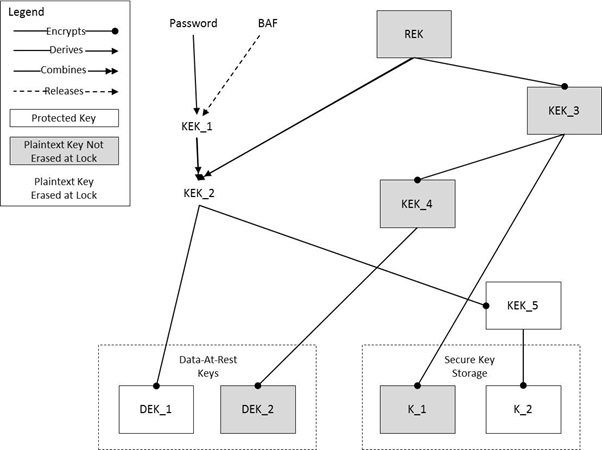
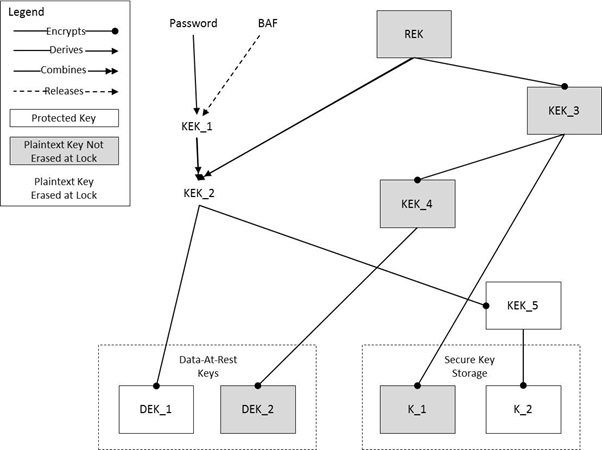
Key Chaining | The method of using multiple layers of encryption keys to protect data. A top layer key encrypts a lower layer key, which encrypts the data; this method can have any number of layers. |
Key Encryption Key (KEK) | A key used to encrypt other keys, such as DEKs or storage that contains keys. |
Liveness Detection | A technique used to ensure that the biometric sample submitted is from an end user. A liveness detection method can help protect the system against some types of spoofing attacks. |
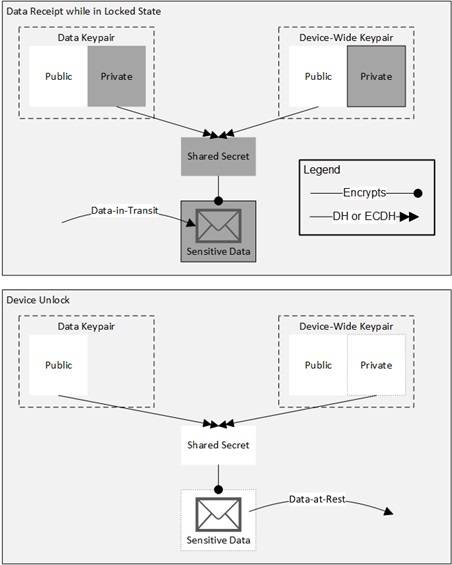
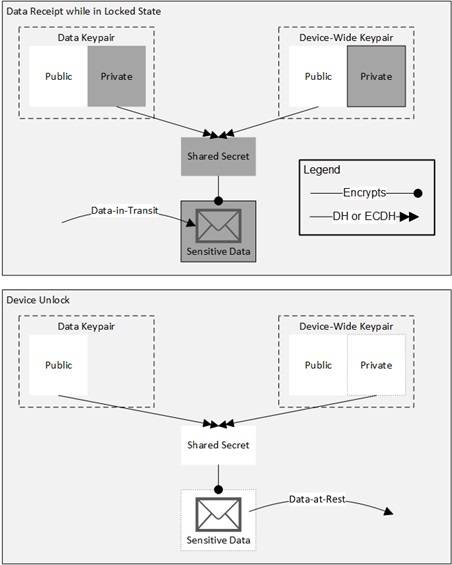
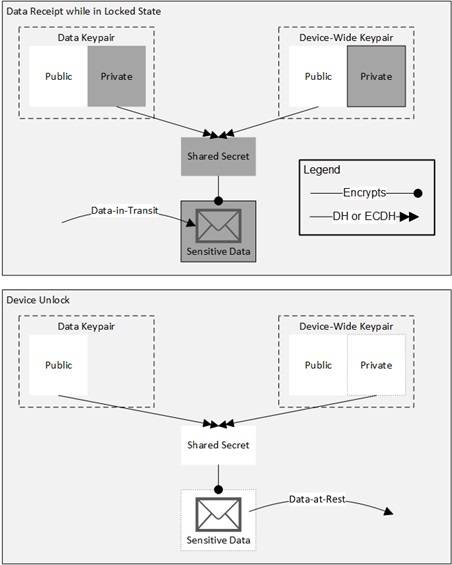
Locked State | Powered on but most functionality is unavailable for use. User authentication is required to access functionality. |
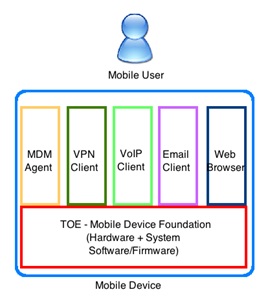
MDM Agent | The MDM Agent is installed on a Mobile Device as an application or is part of the Mobile Device’s OS. The MDM Agent establishes a secure connection back to the MDM Server controlled by the administrator. |
Minutia Point | Friction ridge characteristics that are used to individualize a fingerprint image. Minutia are the points where friction ridges begin, terminate, or split into two or more ridges. In many fingerprint systems, the minutia points are compared for recognition purposes. |
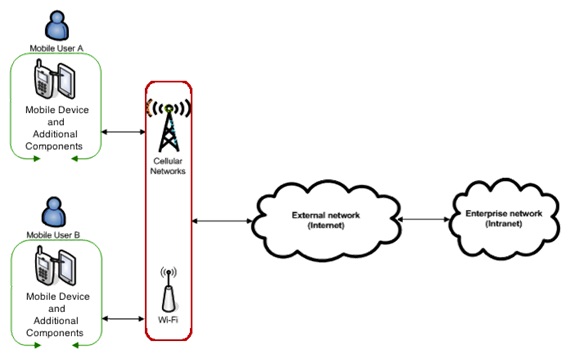
Mobile Device (MD) | A device which is composed of a hardware platform and its system software. The device typically provides wireless connectivity and may include software for functions like secure messaging, email, web, VPN (Virtual Private Network) connection, and VoIP (Voice over IP), for access to the protected enterprise network, enterprise data and applications, and for communicating to other Mobile Devices. |
Mobile Device Management (MDM) | Mobile device management (MDM) products allow enterprises to apply security policies to mobile devices. This system consists of two primary components: the MDM Server and the MDM Agent. |
Mobile Device User (User) | The individual authorized to physically control and operate the Mobile Device. Depending on the use case, this can be the device owner or an individual authorized by the device owner. |
Modality (Biometrics) | A type or class of biometric system, such as fingerprint recognition, facial recognition, iris recognition, voice recognition, signature/sign, and others. |
Mutable Hardware Key | These keys are stored as hardware-protected raw key and can be changed or sanitized. |
| A machine-learning algorithm that
reflects the predictive positive or negative contribution of an individual sample to the
overall performance of a fingerprint matching system. NFIQ 1.0 scores are calculated on a scale from 1 to 5, where NFIQ = 1 indicates high quality samples and NFIQ = 5 indicates poor quality samples [NFIQ 1.0]. NFIQ 2.0 scores are calculated on a scale from 0 to 100, where NFIQ = 0 indicates poor quality samples and NFIQ = 100 indicates high quality samples [NFIQ 2.0]. | |
Operating System (OS) | Software that runs at the highest privilege level and can directly control hardware resources. Modern Mobile Devices typically have at least two primary operating systems: one, which runs on the application processor and one, which runs on the cellular baseband processor. The OS of the application processor handles most user interactions and provides the execution environment for apps. The OS of the cellular baseband processor handles communications with the cellular network and may control other peripherals. The term OS, without context, may be assumed to refer to the OS of the application processor. |
Password Authentication Factor | A type of authentication factor requiring the user to provide a secret set of characters to gain access. |
PIN Authentication Factor | A PIN is a set of numeric or alphabetic characters that may be used in addition to a biometric factor to provide a hybrid authentication factor. At this time it is not considered as a stand-alone authentication mechanism. A PIN is distinct from a password in that the allowed character set and required length of a PIN is typically smaller than that of a password as it is designed to be input quickly. |
Powered Off State | The device has been shut down such that no TOE function can be performed. |
Presentation Attack Detection (PAD) | A technique used to ensure that the biometric sample submitted is from an end user. A presentation attack detection method can help protect the system against some types of spoofing attacks. |
Protected Data (PD) | Protected data is all non-TSF data, including all user or enterprise data. Some or all of this data may be considered sensitive data as well. |
Root Encryption Key (REK) | A key tied to the device used to encrypt other keys. |
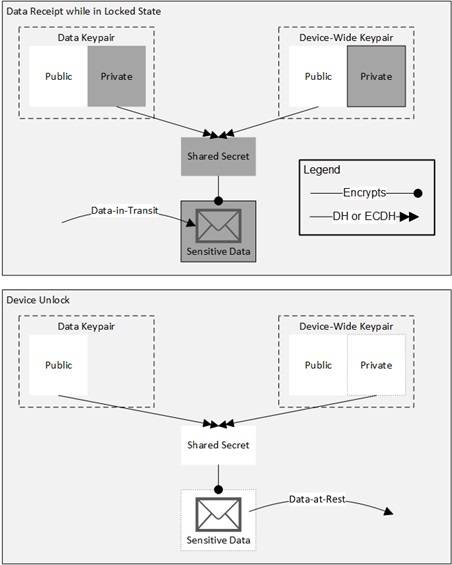
Sensitive data | Sensitive data shall be identified in the TSS section of the Security Target (ST) by the ST author. Sensitive data is a subset or all of the Protected data. Sensitive data may include all user or enterprise data or may be specific application data such as emails, messaging, documents, calendar items, and contacts. Sensitive data is protected while in the locked state (FDP_DAR_EXT.2). |
Software Keys | The OS access the raw bytes of these keys during runtime. |
Template (Biometrics) | A digital representation of an individual’s distinct characteristics, representing information extracted from a biometric sample. This PP further defines enrollment templates and authentication templates. |
Threshold | A user setting for biometric systems operating in verification. Thresholds are also used in enrollment if enrollment templates are created and compared to each other. The acceptance or rejection of biometric data in verification is dependent on the match score falling above or below the threshold. The threshold is adjustable so that the biometric system can be more or less strict, depending on the requirements of any given biometric application. |
Trust Anchor Database | A list of trusted root Certificate Authority certificates. |
TSF Data | Data for the operation of the TSF upon which the enforcement of the requirements relies. |
Unenrolled State | The state in which the Mobile Device is not managed. |
Unlocked State | Powered on and device functionality is available for use. Implies user authentication has occurred (when so configured). |
Verification (Biometrics) | A task where the biometric system attempts to confirm an individual’s claimed identity by comparing a submitted sample to one or more previously enrolled authentication templates. |
| Threat, Assumption, or OSP | Security Objectives | Rationale |
| T.NETWORK_EAVESDROP | O.PROTECTED_COMMS | The threat T.NETWORK_EAVESDROP is countered by O.PROTECTED_COMMS as this provides the capability to communicate using one (or more) standard protocols as a means to maintain the confidentiality of data that are transmitted outside of the TOE. |
| O.CONFIG | The threat T.NETWORK_EAVESDROP is countered by O.CONFIG as this provides a secure configuration of the mobile device to protect data that it processes. | |
| O.AUTH | The threat T.NETWORK_EAVESDROP is countered by O.AUTH as this provides authentication of the endpoints of a trusted communication path. | |
| T.NETWORK_ATTACK | O.PROTECTED_COMMS | The threat T.NETWORK_ATTACK is countered by O.PROTECTED_COMMS as this provides the capability to communicate using one (or more) standard protocols as a means to maintain the confidentiality of data that are transmitted outside of the TOE. |
| O.CONFIG | The threat T.NETWORK_ATTACK is countered by O.CONFIG as this provides a secure configuration of the mobile device to protect data that it processes. | |
| O.AUTH | The threat T.NETWORK_ATTACK is countered by O.AUTH as this provides authentication of the endpoints of a trusted communication path. | |
| T.PHYSICAL_ACCESS | O.STORAGE | The threat T.PHYSICAL_ACCESS is countered by O.STORAGE as this provides the capability to encrypt all user and enterprise data and authentication keys to ensure the confidentiality of data that it stores. |
| O.AUTH | The threat T.PHYSICAL_ACCESS is countered by O.AUTH as this provides the capability to authenticate the user prior to accessing protected functionality and data. | |
| T.MALICIOUS_APP | O.PROTECTED_COMMS | The threat T.MALICIOUS_APP is countered by O.PROTECTED_COMMS as this provides the capability to communicate using one (or more) standard protocols as a means to maintain the confidentiality of data that are transmitted outside of the TOE. |
| O.CONFIG | The threat T.MALICIOUS_APP is countered by O.CONFIG as this provides the capability to configure and apply security policies to ensure the Mobile Device can protect user and enterprise data that it may store or process. | |
| O.AUTH | The threat T.MALICIOUS_APP is countered by O.AUTH as this provides the capability to authenticate the user and endpoints of a trusted path to ensure they are communicating with an authorized entity with appropriate privileges. | |
| O.INTEGRITY | The threat T.MALICIOUS_APP is countered by O.INTEGRITY as this provides the capability to perform self-tests to ensure the integrity of critical functionality, software/firmware and data has been maintained. | |
| O.PRIVACY | The threat T.MALICIOUS_APP is countered by O.PRIVACY as this provides separation and privacy between user activities. | |
| T.PERSISTENT_PRESENCE | O.INTEGRITY | The threat T.PERSISTENT_PRESENCE is countered by O.INTEGRITY as this provides the capability to perform self-tests to ensure the integrity of critical functionality, software/firmware and data has been maintained. |
| O.PRIVACY | The threat T.PERSISTENT_PRESENCE is countered by O.PRIVACY as this provides separation and privacy between user activities. | |
| A.CONFIG | OE.CONFIG | The operational environment objective OE.CONFIG is realized through A.CONFIG. |
| A.NOTIFY | OE.NOTIFY | The operational environment objective OE.NOTIFY is realized through A.NOTIFY. |
| A.PRECAUTION | OE.PRECAUTION | The operational environment objective OE.PRECAUTION is realized through A.PRECAUTION. |
| A.PROPER_USER | OE.DATA_PROPER_USER | The operational environment objective OE.DATA_PROPER_USER is realized through A.PROPER_USER. |
| Requirement | Auditable Events | Additional Audit Record Contents |
| FAU_GEN.1 | None. | |
| FAU_STG.1 | None. | |
| FAU_STG.4 | None. | |
| FCS_CKM_EXT.1 | [selection: generation of a REK, None]. | No additional information. |
| FCS_CKM_EXT.2 | None. | |
| FCS_CKM_EXT.3 | None. | |
| FCS_CKM_EXT.4 | None. | |
| FCS_CKM_EXT.5 | [selection: Failure of the wipe, None]. | No additional information. |
| FCS_CKM_EXT.6 | None. | |
| FCS_CKM.1 | [selection: Failure of key generation activity for authentication keys, None]. | No additional information. |
| FCS_CKM.2/UNLOCKED | None. | |
| FCS_CKM.2/LOCKED | None. | |
| FCS_COP.1/ENCRYPT | None. | |
| FCS_COP.1/HASH | None. | |
| FCS_COP.1/SIGN | None. | |
| FCS_COP.1/KEYHMAC | None. | |
| FCS_COP.1/CONDITION | None. | |
| FCS_IV_EXT.1 | None. | |
| FCS_SRV_EXT.1 | None. | |
| FCS_STG_EXT.1 | Import or destruction of key. | Identity of key. Role and identity of requester. |
| [selection: Exceptions to use and destruction rules, No other events] | ||
| FCS_STG_EXT.2 | None. | |
| FCS_STG_EXT.3 | Failure to verify integrity of stored key. | Identity of key being verified. |
| FDP_DAR_EXT.1 | [selection: Failure to encrypt/decrypt data, None]. | No additional information. |
| FDP_DAR_EXT.2 | Failure to encrypt/decrypt data. | No additional information. |
| FDP_IFC_EXT.1 | None. | |
| FDP_STG_EXT.1 | Addition or removal of certificate from Trust Anchor Database. | Subject name of certificate. |
| FIA_PMG_EXT.1 | None. | |
| FIA_TRT_EXT.1 | None. | |
| FIA_UAU_EXT.1 | None. | |
| FIA_UAU.5 | None. | |
| FIA_UAU.7 | None. | |
| FIA_X509_EXT.1 | Failure to validate X.509v3 certificate. | Reason for failure of validation. |
| FMT_MOF_EXT.1 | None. | |
| FPT_AEX_EXT.1 | None. | |
| FPT_AEX_EXT.2 | None. | |
| FPT_AEX_EXT.3 | None. | |
| FPT_JTA_EXT.1 | None. | |
| FPT_KST_EXT.1 | None. | |
| FPT_KST_EXT.2 | None. | |
| FPT_KST_EXT.3 | None. | |
| FPT_NOT_EXT.1 | [selection: Measurement of TSF software, None]. | [selection: Integrity verification value, No additional information]. |
| FPT_STM.1 | None. | |
| FPT_TST_EXT.1 | Initiation of self-test. | [selection: Algorithm that caused the failure, none] |
| Failure of self-test. | ||
| FPT_TST_EXT.2/PREKERNEL | Start-up of TOE. | No additional information. |
| [selection: Detected integrity violation, none] | [selection: The TSF code file that caused the integrity violation, No additional information] | |
| FPT_TUD_EXT.1 | None. | |
| FTA_SSL_EXT.1 | None. |
| Requirement | Auditable Events | Additional Audit Record Contents |
| FAU_SAR.1 | None. | |
| FAU_SEL.1 | All modifications to the audit configuration that occur while the audit collection functions are operating. | No additional information. |
| FCS_CKM_EXT.7 | None. | |
| FCS_DTLS_EXT.1 (TLS Package) | Failure of the certificate validity check. | Issuer Name and Subject Name of certificate. |
| FCS_HTTPS_EXT.1 | Failure of the certificate validity check. | Issuer Name and Subject Name of certificate. [selection: User’s authorization decision, No additional information]. |
| FCS_RBG_EXT.1 | Failure of the randomization process. | No additional information. |
| FCS_RBG_EXT.2 | None. | |
| FCS_RBG_EXT.3 | None. | |
| FCS_SRV_EXT.2 | None. | |
| FCS_TLSC_EXT.1 (TLS Package) | Establishment/termination of a TLS session. | Non-TOE endpoint of connection. |
| Failure to establish a TLS session. | Reason for failure. | |
| Failure to verify presented identifier. | Presented identifier and reference identifier. | |
| FCS_TLSC_EXT.2 (TLS Package) | None. | |
| FCS_TLSC_EXT.3 (TLS Package) | None. | |
| FDP_ACF_EXT.1 | None. | |
| FDP_ACF_EXT.2 | None. | |
| FDP_ACF_EXT.3 | None. | |
| FDP_BCK_EXT.1 | None. | |
| FDP_PBA_EXT.1 | None. | |
| FDP_UPC_EXT.1/APPS | Application initiation of trusted channel. | Name of application. Trusted channel protocol. Non-TOE endpoint of connection. |
| FDP_UPC_EXT.1/BLUETOOTH | Application initiation of trusted channel. | Name of application. Trusted channel protocol. Non-TOE endpoint of connection. |
| FIA_AFL_EXT.1 | Excess of authentication failure limit. | Authentication factor used. |
| FIA_BMG_EXT.1 | None. | |
| FIA_BMG_EXT.2 | None. | |
| FIA_BMG_EXT.3 | None. | |
| FIA_BMG_EXT.4 | None. | |
| FIA_BMG_EXT.5 | None. | |
| FIA_BMG_EXT.6 | None. | |
| FIA_UAU_EXT.2 | Action performed before authentication. | No additional information. |
| FIA_UAU.6 | User changes Password Authentication Factor. | No additional information. |
| FIA_UAU_EXT.4 | None. | |
| FIA_X509_EXT.2 | Failure to establish connection to determine revocation status. | No additional information. |
| FIA_X509_EXT.3 | None. | |
| FIA_X509_EXT.4 | Generation of Certificate Enrollment Request. | Issuer and Subject name of EST Server. Method of authentication. Issuer and Subject name of certificate used to authenticate. Content of Certificate Request Message. |
| Success or failure of enrollment. | Issuer and Subject name of added certificate or reason for failure. | |
| Update of EST Trust Anchor Database | Subject name of added Root CA. | |
| FIA_X509_EXT.5 | None. | |
| FMT_SMF_EXT.1 | [selection: Initiation of policy update, none]. | [selection: Policy name, none]. |
| [selection: Change of settings, none] | [selection: Role of user that changed setting, Value of new setting, none]. | |
| [selection: Success or failure of function, none] | [selection: Role of user that performed function, Function performed, Reason for failure, none]. | |
| Initiation of software update. | Version of update. | |
| Initiation of application installation or update. | Name and version of application. | |
| FMT_SMF_EXT.2 | [selection: Unenrollment, Initiation of unenrollment, none] | [selection: Identity of administrator Remediation action performed, failure of accepting command to unenroll, none] |
| FMT_SMF_EXT.3 | None. | |
| FPT_AEX_EXT.4 | None. | |
| FPT_AEX_EXT.5 | None. | |
| FPT_AEX_EXT.6 | None. | |
| FPT_AEX_EXT.7 | None. | |
| FPT_BBD_EXT.1 | None. | |
| FPT_BLT_EXT.1 | None. | |
| FPT_NOT_EXT.2 | None. | |
| FPT_TST_EXT.2/POSTKERNEL | [selection: Detected integrity violation, none] | [selection: The TSF code file that caused the integrity violation, No additional information] |
| FPT_TST_EXT.3 | None. | |
| FPT_TUD_EXT.2 | Success or failure of signature verification for software updates. | No additional information. |
| FPT_TUD_EXT.3 | Success or failure of signature verification for applications. | No additional information. |
| FPT_TUD_EXT.4 | None. | |
| FPT_TUD_EXT.5 | None. | |
| FPT_TUD_EXT.6 | None. | |
| FTA_TAB.1 | None. | |
| FTP_ITC_EXT.1 | Initiation and termination of trusted channel. | Trusted channel protocol. Non-TOE endpoint of connection. |
A subset of the User Data Protection focuses on protecting Data-At-Rest, namely FDP_DAR_EXT.1 and FDP_DAR_EXT.2. Three levels of data-at-rest protection are addressed: TSF data, Protected Data (and keys), and sensitive data. Table 6 addresses the level of protection required for each level of data-at-rest.
Table 6: : Protection of Data Levels| Data Level | Protection Required |
| TSF Data | TSF data does not require confidentiality, but does require integrity protection. (FPT_TST_EXT.2/PREKERNEL) |
| Protected Data | Protected data is encrypted while powered off. (FDP_DAR_EXT.1) |
| Sensitive Data | Sensitive data is encrypted while in the locked state, in addition to while powered off. (FDP_DAR_EXT.2) |
| # | Management Function | Impl. | User Only | Admin | Admin Only |
| 1 |
configure password policy:
| MMandatory | -N/A | MMandatory | MMandatory |
| 2 |
configure session
locking policy:
| MMandatory | -N/A | MMandatory | MMandatory |
| 3 |
enable/disable the VPN
protection:
[selection: b. on a per-app basisc. on a per-group of applications processes basisd. no other method]
| MMandatory | OOptional | OOptional | OOptional |
| 4 | enable/disable [assignment: list of all radios] | MMandatory | OOptional | OOptional | OOptional |
| 5 |
enable/disable
[assignment: list of audio or visual collection devices]:
[selection: b. on a per-app basisc. on a per-group of applications processes basisd. no other method]
| MMandatory | OOptional | OOptional | OOptional |
| 6 | transition to the locked state | MMandatory | -N/A | MMandatory | -N/A |
| 7 | TSF wipe of protected data | MMandatory | -N/A | MMandatory | -N/A |
| 8 |
configure
application installation policy by [selection: a. restricting the sources of applicationsb. specifying a set of allowed applications based on
[assignment: application characteristics] (an application allowlist)c. denying installation of applications]
| MMandatory | -N/A | MMandatory | MMandatory |
| 9 | import keys/secrets into the secure key storage | MMandatory | OOptional | OOptional | -N/A |
| 10 | destroy imported keys/secrets and [selection: no other keys/secrets, [assignment: list of other categories of keys/secrets]] in the secure key storage | MMandatory | OOptional | OOptional | -N/A |
| 11 | import X.509v3 certificates into the Trust Anchor Database | MMandatory | -N/A | MMandatory | OOptional |
| 12 | remove imported X.509v3 certificates and [selection: no other X.509v3 certificates, [assignment: list of other categories of X.509v3 certificates]] in the Trust Anchor Database | MMandatory | OOptional | OOptional | -N/A |
| 13 | enroll the TOE in management | MMandatory | OOptional | OOptional | OOptional |
| 14 | remove applications | MMandatory | -N/A | MMandatory | OOptional |
| 15 | update system software | MMandatory | -N/A | MMandatory | OOptional |
| 16 | install applications | MMandatory | -N/A | MMandatory | OOptional |
| 17 | remove Enterprise applications | MMandatory | -N/A | MMandatory | -N/A |
| 18 | enable/disable display notification in the locked state of: [selection: a. email notificationsb. calendar appointmentsc. contact associated with phone call notificationd. text message notificatione. other application-based notificationsf. all notifications] | MMandatory | OOptional | OOptional | OOptional |
| 19 | enable data-at rest protection | MMandatory | OOptional | OOptional | OOptional |
| 20 | enable removable media’s data-at-rest protection | MMandatory | OOptional | OOptional | OOptional |
| 21 |
enable/disable location
services:
[selection: b. on a per-app basisc. on a per-group of applications processes basisd. no other method]
| MMandatory | OOptional | OOptional | OOptional |
| 22 | enable/disable the use of [selection: Biometric Authentication Factor, Hybrid Authentication Factor] | MMandatory | OOptional | OOptional | OOptional |
| 23 | configure whether to allow/disallow establishment of a trusted channel if the peer/server certificate is deemed invalid. | MMandatory | OOptional | OOptional | OOptional |
| 24 | enable/disable all data signaling over [assignment: list of externally accessible hardware ports] | OOptional | OOptional | OOptional | OOptional |
| 25 | enable/disable [assignment: list of protocols where the device acts as a server] | OOptional | OOptional | OOptional | OOptional |
| 26 | enable/disable developer modes | OOptional | OOptional | OOptional | OOptional |
| 27 | enable/disable bypass of local user authentication | OOptional | OOptional | OOptional | OOptional |
| 28 | wipe Enterprise data | OOptional | OOptional | OOptional | -N/A |
| 29 | approve [selection: import, removal] by applications of X.509v3 certificates in the Trust Anchor Database | OOptional | OOptional | OOptional | OOptional |
| 30 | configure whether to allow/disallow establishment of a trusted channel if the TSF cannot establish a connection to determine the validity of a certificate | OOptional | OOptional | OOptional | OOptional |
| 31 | enable/disable the cellular protocols used to connect to cellular network base stations | OOptional | OOptional | OOptional | OOptional |
| 32 | read audit logs kept by the TSF | OOptional | OOptional | OOptional | -N/A |
| 33 | configure [selection: certificate, public-key] used to validate digital signature on applications | OOptional | OOptional | OOptional | OOptional |
| approve exceptions for shared use of keys/secrets by multiple applications | OOptional | OOptional | OOptional | OOptional | |
| 35 | approve exceptions for destruction of keys/secrets by applications that did not import the key/secret | OOptional | OOptional | OOptional | OOptional |
| 36 | configure the unlock banner | OOptional | -N/A | OOptional | OOptional |
| 37 | configure the auditable items | OOptional | -N/A | OOptional | OOptional |
| 38 | retrieve TSF-software integrity verification values | OOptional | OOptional | OOptional | OOptional |
| 39 | enable/disable [selection: USB mass storage modeUSB data transfer without user authenticationUSB data transfer without authentication of the connecting system] | OOptional | OOptional | OOptional | OOptional |
| 40 | enable/disable backup of [selection: all applications, selected applications, selected groups of applications, configuration data] to [selection: locally connected system, remote system] | OOptional | OOptional | OOptional | OOptional |
| 41 | enable/disable [selection: Hotspot functionality authenticated by [selection: pre-shared key, passcode, no authentication]USB tethering authenticated by [selection: pre-shared key, passcode, no authentication] ] | OOptional | OOptional | OOptional | OOptional |
| 42 | approve exceptions for sharing data between [selection: applications, groups of applications] | OOptional | OOptional | OOptional | OOptional |
| 43 | place applications into application groups based on [assignment: enterprise configuration settings] | OOptional | OOptional | OOptional | OOptional |
| 44 | unenroll the TOE from management | OOptional | OOptional | OOptional | OOptional |
| 45 |
enable/disable the
Always On VPN protection:
[selection: b. on a per-app basisc. on a per-group of applications processes basisd. no other method]
| OOptional | OOptional | OOptional | OOptional |
| 46 | revoke Biometric template | OOptional | OOptional | OOptional | OOptional |
| 47 | [assignment: list of other management functions to be provided by the TSF] | OOptional | OOptional | OOptional | OOptional |
Regarding functions 4 and 5, disablement of a particular radio or audio/visual device must be effective as soon as the TOE has power. Disablement must also apply when the TOE is booted into auxiliary boot modes, for example, associated with updates or backup. If the TOE supports states in which security management policy is inaccessible, for example, due to data-at-rest protection, it is acceptable to meet this requirement by ensuring that these devices are disabled by default while in these states. That these devices are disabled during auxiliary boot modes does not imply that the device (particularly the cellular radio) may not be enabled in order to perform emergency phone calls.
Wipe of the TSF (function 7) is performed according to FCS_CKM_EXT.5. Protected data is all non-TSF data, including all user or enterprise data. Some or all of this data may be considered sensitive data as well. The selection in function 8 allows the ST author to select which mechanisms are available to the administrator through the MDM Agent to restrict the applications which the user may install. The ST author must state if application allowlist is applied device-wide or if it can be specified to apply to either the Enterprise and/or Personal applications.The following rationale provides justification for each security objective for the TOE, showing that the SFRs are suitable to meet and achieve the security objectives:
| Objective | Addressed by | Rationale |
|---|---|---|
| O.PROTECTED_COMMS | FCS_CKM.1 | FCS_CKM.1 supports the objective by defining the key generation algorithms that are used for protected communications. |
| FCS_CKM.2/UNLOCKED | FCS_CKM.2/UNLOCKED supports the objective by defining the key establishment algorithms that are used for protected communications. | |
| FCS_CKM_EXT.8 (Bluetooth Module) | FCS_CKM_EXT.8 supports the objective by requiring the TSF to perform key rotation for Bluetooth to limit the window of opportunity for an attacker to determine the key value. | |
| FCS_COP.1/ENCRYPT | FCS_COP.1/ENCRYPT supports the objective by requiring the TSF to implement symmetric encryption algorithms that are used in support of protected communications. | |
| FCS_COP.1/HASH | FCS_COP.1/HASH supports the objective by requiring the TSF to implement hash algorithms that are used in support of protected communications. | |
| FCS_COP.1/SIGN | FCS_COP.1/SIGN supports the objective by requiring the TSF to implement digital signature algorithms that are used in support of protected communications. | |
| FCS_COP.1/KEYHMAC | FCS_COP.1/KEYHMAC supports the objective by requiring the TSF to implement HMAC algorithms that are used in support of protected communications. | |
| FCS_DTLSC_EXT.1 (TLS Package) | FCS_DTLSC_EXT.1 supports the objective by defining the TOE's implementation of DTLS as a client if this protocol is used for protected communications. | |
| FCS_DTLSC_EXT.2 (TLS Package) | FCS_DTLSC_EXT.2 supports the objective by defining the TOE's implementation of mutually-authenticated DTLS as a client if this protocol is used for protected communications. | |
| FCS_HTTPS_EXT.1 | FCS_HTTPS_EXT.1 supports the objective by defining the TOE's implementation of HTTPS if this protocol is used for protected communications. | |
| FCS_RBG_EXT.1 | FCS_RBG_EXT.1 supports the objective by requiring the TSF to implement deterministic random bit generation algorithms that are used in support of protected communications. | |
| FCS_RBG_EXT.2 (Objective) | FCS_RBG_EXT.2 supports the objective by requiring the TSF to save the DRBG state between reboots to ensure availability of this service. | |
| FCS_RBG_EXT.3 (Objective) | FCS_RBG_EXT.3 supports the objective by defining the TSF's implementation of the SP 800-90A Personalization String for applications that require this. | |
| FCS_SRV_EXT.1 | FCS_SRV_EXT.1 supports the objective by defining the cryptographic services that the TSF must make available to third-party applications, which includes those that can support protected communications. | |
| FCS_SRV_EXT.2 (Objective) | FCS_SRV_EXT.2 supports the objective by requiring the TSF to make keys in its secure key storage available for use in encryption and signing operations. | |
| FCS_TLSC_EXT.1 (TLS Package) | FCS_TLSC_EXT.1 supports the objective by defining the TOE's implementation of TLS as a client for protected communications. | |
| FCS_TLSC_EXT.2 (TLS Package) | FCS_TLSC_EXT.2 supports the objective by defining the TOE's implementation of mutually-authenticated TLS as a client for protected communications. | |
| FCS_TLSC_EXT.3 (TLS Package) | FCS_TLSC_EXT.3 supports the objective by requiring the TSF to support the TLS signature algorithms extension as part of establishing TLS protected communications. | |
| FDP_BLT_EXT.1 | FDP_BLT_EXT.1 supports the objective by limiting the applications that are authorized to use the Bluetooth interface, which may include a trusted channel. | |
| FDP_IFC_EXT.1 | FDP_IFC_EXT.1 supports the objective by requiring the TSF to have either its own IPsec VPN client or interface that allows a third-party VPN client to be deployed on it. | |
| FDP_STG_EXT.1 | FDP_STG_EXT.1 supports the objective by requiring the TSF to implement a protected key storage that can be used to protect persistent keys used for protected communications from disclosure. | |
| FDP_UPC_EXT.1/APPS | FDP_UPC_EXT.1/APPS supports the objective by defining the protected communications channels that it allows third-party applications to invoke. | |
| FDP_UPC_EXT.1/BLUETOOTH | FDP_UPC_EXT.1/BLUETOOTH supports the objective by defining the Bluetooth interfaces that it allows third-party applications to invoke. | |
| FIA_BLT_EXT.1 (Bluetooth Module) | FIA_BLT_EXT.1 supports the objective by ensuring that Bluetooth communications are not initiated without user approval. | |
| FIA_BLT_EXT.2 (Bluetooth Module) | FIA_BLT_EXT.2 supports the objective by requiring the TSF to implement Bluetooth mutual authentication. | |
| FIA_BLT_EXT.3 (Bluetooth Module) | FIA_BLT_EXT.3 supports the objective by preventing Bluetooth spoofing by rejecting connections with duplicate device addresses. | |
| FIA_BLT_EXT.4 (Bluetooth Module) | FIA_BLT_EXT.4 supports the objective by defining the TSF's implementation of Bluetooth Secure Simple Pairing. | |
| FIA_BLT_EXT.5 (Bluetooth Module) | FIA_BLT_EXT.5 supports the objective by requiring the TSF to support Secure Connections Only mode for the supported Bluetooth communication channels. | |
| FIA_BLT_EXT.6 (Bluetooth Module) | FIA_BLT_EXT.6 supports the objective by requiring the TSF to specify the Bluetooth profiles that it requires explicit user authorization to grant access to for trusted devices. | |
| FIA_BLT_EXT.7 (Bluetooth Module) | FIA_BLT_EXT.7 supports the objective by requiring the TSF to specify the Bluetooth profiles that it requires explicit user authorization to grant access to for untrusted devices. | |
| FIA_X509_EXT.1 | FIA_X509_EXT.1 supports the objective by defining the rules the TSF uses to determine if a presented X.509 certificate is valid. | |
| FIA_X509_EXT.2 | FIA_X509_EXT.2 supports the objective by requiring the TSF to enumerate its uses of X.509 certificates (including protected communications) and its behavior when a certificate's revocation status is undetermined. | |
| FIA_X509_EXT.3 | FIA_X509_EXT.3 supports the objective by requiring the TSF to provide a certificate validation service to third-party applications. | |
| FIA_X509_EXT.4 (Objective) | FIA_X509_EXT.4 supports the objective by defining the implementation of EST as a method by which the TSF can obtain an X.509 certificate for its own use. | |
| FIA_X509_EXT.5 (Objective) | FIA_X509_EXT.5 supports the objective by defining the implementation of Certificate Request Messages as a method by which the TSF can obtain an X.509 certificate for its own use. | |
| FPT_BLT_EXT.1 (Objective) | FPT_BLT_EXT.1 supports the objective by requiring the TSF to disable certain Bluetooth profiles when they are inactive such that explicit user authorization is required to re-enable them. | |
| FTP_BLT_EXT.1 (Bluetooth Module) | FTP_BLT_EXT.1 supports the objective by requiring the TSF to implement encryption to protect Bluetooth communications | |
| FTP_BLT_EXT.2 (Bluetooth Module) | FTP_BLT_EXT.2 supports the objective by requiring the TSF to prevent data transmission over Bluetooth if the paired device is not using encryption. | |
| FTP_BLT_EXT.3/BR (Bluetooth Module) | FTP_BLT_EXT.3/BR supports the objective by defining the minimum key size for Bluetooth BR/EDR communications. | |
| FTP_BLT_EXT.3/LE (Bluetooth Module) | FTP_BLT_EXT.3/LE supports the objective by defining the minimum key size for Bluetooth LE communications. | |
| FTP_ITC_EXT.1 | FTP_ITC_EXT.1 supports the objective by defining the protected communications protocols that the TSF implements. | |
| O.STORAGE | FCS_CKM.2/LOCKED | |
| FCS_CKM_EXT.1 | FCS_CKM_EXT.1 supports the objective by defining the TOE's root encryption key that is used to protect data at rest. | |
| FCS_CKM_EXT.2 | FCS_CKM_EXT.2 supports the objective by defining how the TSF creates data encryption keys that are used to protect data at rest. | |
| FCS_CKM_EXT.3 | FCS_CKM_EXT.3 supports the objective by defining the key encryption keys the TOE uses to protect data at rest and how they are created. | |
| FCS_CKM_EXT.4 | FCS_CKM_EXT.4 supports the objective by requiring the TSF to destroy keys and key material that could otherwise be used to compromise data at rest. | |
| FCS_CKM_EXT.5 | FCS_CKM_EXT.5 supports the objective by defining the mechanism the TSF uses to perform a wipe operation that securely destroys data at rest. | |
| FCS_CKM_EXT.6 | FCS_CKM_EXT.6 supports the objective by requiring the TSF to use secure salts when performing cryptographic operations that require them. | |
| FCS_CKM_EXT.7 (Sel-Based) | FCS_CKM_EXT.7 supports the objective by ensuring that the TOE's root encryption key cannot be disclosed. | |
| FCS_COP.1/ENCRYPT | FCS_COP.1/ENCRYPT supports the objective by defining a symmetric encryption/decryption function that can be used to protect data at rest. | |
| FCS_COP.1/HASH | FCS_COP.1/HASH supports the objective by defining a hash function that can be used to protect data at rest. | |
| FCS_COP.1/SIGN | FCS_COP.1/SIGN supports the objective by defining a digital signature function that can be used to protect data at rest. | |
| FCS_COP.1/KEYHMAC | FCS_COP.1/KEYHMAC supports the objective by defining an HMAC function that can be used to protect data at rest. | |
| FCS_COP.1/CONDITION | FCS_COP.1/CONDITION supports the objective by defining a key derivation function that can be used to protect data at rest. | |
| FCS_IV_EXT.1 | FCS_IV_EXT.1 supports the objective by ensuring that any IVs the TSF generates for AES keys are generated in an appropriate manner based on the relevant standards. | |
| FCS_RBG_EXT.1 | FCS_RBG_EXT.1 supports the objective by defining random bit generation function that can be used to protect data at rest. | |
| FCS_STG_EXT.1 | FCS_STG_EXT.1 supports the objective by requiring the TSF to implement a hardware or software key store to protect key data at rest. | |
| FCS_STG_EXT.2 | FCS_STG_EXT.2 supports the objective by defining the confidentiality mechanism used to protect stored key data from unauthorized disclosure. | |
| FCS_STG_EXT.3 | FCS_STG_EXT.3 supports the objective by defining the integrity mechanism used to protect stored key data from unauthorized modification. | |
| FDP_ACF_EXT.3 (Objective) | FDP_ACF_EXT.3 supports the objective by ensuring that the TSF does not permit write and execute permissions on stored data to be granted simultaneously. | |
| FDP_DAR_EXT.1 | FDP_DAR_EXT.1 supports the objective by requiring the TSF to encrypt all sensitive data using data encryption keys. | |
| FDP_DAR_EXT.2 | FDP_DAR_EXT.2 supports the objective by requiring the TSF to provide a mechanism to mark data as sensitive so that it can subject to encryption. | |
| FIA_UAU_EXT.1 | FIA_UAU_EXT.1 supports the objective by requiring the presentation of a valid authorization factor in order to decrypt sensitive data at rest. | |
| FPT_KST_EXT.1 | FPT_KST_EXT.1 supports the objective by requiring the TSF to prevent the storage of plaintext key data in readable non-volatile memory. | |
| FPT_KST_EXT.2 | FPT_KST_EXT.2 supports the objective by requiring the TSF to prevent any transmission of plaintext key material outside of the TOE boundary. | |
| FPT_KST_EXT.3 | FPT_KST_EXT.3 supports the objective by requiring the TSF to prevent export of any stored plaintext keys. | |
| FPT_JTA_EXT.1 | FPT_JTA_EXT.1 supports the objective by requiring the TSF to enforce access controls against JTAG so that this interface cannot be used to disclose data at rest. | |
| O.CONFIG | FMT_MOF_EXT.1 | FMT_MOF_EXT.1 supports the objective by specifying the TSF management functions that an end user is authorized to perform. |
| FMT_SMF_EXT.1 | FMT_SMF_EXT.1 supports the objective by defining the TSF management functions and the users or roles that are authorized to invoke them. | |
| FMT_SMF_EXT.2 | FMT_SMF_EXT.2 supports the objective by defining the configuration actions that the TSF performs automatically upon unenrollment from mobile device management. | |
| FTA_TAB.1 (Objective) | FTA_TAB.1 supports the objective by requiring the TSF to display a warning banner to users that governs authorized usage of the TOE. | |
| O.AUTH | FDP_PBA_EXT.1 (Sel-Based) | FDP_PBA_EXT.1 supports the objective by defining the mechanism that the TSF uses to protect stored biometric templates. |
| FIA_AFL_EXT.1 | FIA_AFL_EXT.1 supports the objective by defining the authentication mechanisms that are subject to lockout behavior and how the TSF handles repeated failed authentication attempts. | |
| FIA_BLT_EXT.1(Bluetooth Module) | FIA_BLT_EXT.1 supports the objective by requiring a user to authorize all Bluetooth pairings. | |
| FIA_BLT_EXT.2 (Bluetooth Module) | FIA_BLT_EXT.2 supports the objective by requiring the TSF to enforce mutual authentication for Bluetooth. | |
| FIA_BMG_EXT.1 (Sel-Based) | FIA_BMG_EXT.1 supports the objective by defining the minimum accuracy of biometric authentication methods that the TSF must support. | |
| FIA_BMG_EXT.2 (Objective) | FIA_BMG_EXT.2 supports the objective by requiring the TSF to enforce a minimum quality standard on the biometric data used for enrollment. | |
| FIA_BMG_EXT.3 (Objective) | FIA_BMG_EXT.3 supports the objective by defining the quality metrics used by the TSF to enforce minimum quality for biometric data. | |
| FIA_BMG_EXT.4 (Objective) | FIA_BMG_EXT.4 supports the objective by requiring the TSF to generate enrollment and authentication templates using data that exceeds a minimum quality threshold. | |
| FIA_BMG_EXT.5 (Objective) | FIA_BMG_EXT.5 supports the objective by defining how the TSF handles biometric data that does not match expected parameters. | |
| FIA_BMG_EXT.6 (Objective) | FIA_BMG_EXT.6 supports the objective by requiring the TSF to detect spoofed biometric data. | |
| FIA_PMG_EXT.1 | FIA_PMG_EXT.1 supports the objective by defining the minimum quality threshold for passwords that the TSF must enforce. | |
| FIA_TRT_EXT.1 | FIA_TRT_EXT.1 supports the objective by enforcing an authentication throttling mechanism that limits the rate at which authentication attempts can be made to the TOE. | |
| FIA_UAU_EXT.1 | FIA_UAU_EXT.1 supports the objective by requiring the TSF to be provided with a valid password before access to protected data is granted. | |
| FIA_UAU_EXT.2 | FIA_UAU_EXT.2 supports the objective by defining the TOE functions that can be accessed without authentication such that all other services require authentication. | |
| FIA_UAU_EXT.4 (Optional) | FIA_UAU_EXT.4 supports the objective by defining a secondary authentication mechanism for Enterprise resources. | |
| FIA_UAU.5 | FIA_UAU.5 supports the objective by defining all authentication factors the TSF supports and rules for how these authentication factors are used to gain access to the TSF. | |
| FIA_UAU.6 | FIA_UAU.6 supports the objective by requiring the TSF to re-authenticate users with their password prior to allowing them to change any other authentication data. | |
| FIA_UAU.7 | FIA_UAU.7 supports the objective by ensuring that TSF does not disclose user authentication data as it is being input to the TOE. | |
| FIA_X509_EXT.2 | FIA_X509_EXT.2 supports the objective by defining the functions for which the TSF uses X.509 certificates as an authentication mechanism. | |
| FTA_SSL_EXT.1 | FTA_SSL_EXT.1 supports the objective by requiring the TSF to ensure that an idle user session is terminated after a given period of time. | |
| O.INTEGRITY | FAU_GEN.1 | FAU_GEN.1 supports the objective by requiring the TSF to record actions performed against it to establish a record of potential malicious activity. |
| FAU_SAR.1 (Objective) | FAU_SAR.1 supports the objective by requiring the TSF to provide a mechanism to review the stored audit data so administrators can diagnose the root cause of malicious usage. | |
| FAU_SEL.1 (Objective) | FAU_SEL.1 supports the objective by allowing the TSF to restrict the audit records that are generated so that records unrelated to potential malicious usage can be suppressed. | |
| FAU_STG.1 | FAU_STG.1 supports the objective by ensuring that a malicious user cannot tamper with audit records by modifying or deleting them. | |
| FAU_STG.4 | FAU_STG.4 supports the objective by ensuring the availability of audit records. | |
| FCS_COP.1/HASH | FCS_COP.1/HASH supports the objective by requiring the TSF to implement hash algorithms that can be used to assert and verify integrity. | |
| FCS_COP.1/SIGN | FCS_COP.1/SIGN supports the objective by requiring the TSF to implement digital signature algorithms that can be used to assert and verify integrity. | |
| FDP_ACF_EXT.1 | FDP_ACF_EXT.1 supports the objective by requiring the TSF to maintain the integrity of its system services by limiting the entities that can access them. | |
| FDP_ACF_EXT.3 (Objective) | FDP_ACF_EXT.3 supports the objective by requiring the TSF to ensure that writable files cannot be executed and vice versa, such that arbitrary code or scripts cannot be executed to compromise the integrity of the TOE. | |
| FPT_AEX_EXT.1 | FPT_AEX_EXT.1 supports the objective by requiring the TSF to implement ASLR to prevent a compromise of the TSF. | |
| FPT_AEX_EXT.2 | FPT_AEX_EXT.2 supports the objective by requiring the TSF to enforce permissions against memory pages to prevent a compromise of the TSF. | |
| FPT_AEX_EXT.3 | FPT_AEX_EXT.3 supports the objective by requiring the TSF to implement stack overflow protection to prevent a compromise of the TSF. | |
| FPT_AEX_EXT.4 | FPT_AEX_EXT.4 supports the objective by requiring the TSF to enforce address space separation to prevent a compromise of the TSF. | |
| FPT_AEX_EXT.5 (Objective) | FPT_AEX_EXT.5 supports the objective by requiring the TSF to implement ASLR to prevent a compromise of the TSF. | |
| FPT_AEX_EXT.6 (Objective) | FPT_AEX_EXT.6 supports the objective by requiring the TSF to ensure that writable files cannot be executed and vice versa, such that arbitrary code or scripts cannot be executed to compromise the integrity of the TOE. | |
| FPT_AEX_EXT.7 (Objective) | FPT_AEX_EXT.7 supports the objective by requiring the TSF to implement heap overflow protection to prevent a compromise of the TSF. | |
| FPT_BBD_EXT.1 (Objective) | FPT_BBD_EXT.1 supports the objective by ensuring that isolation between the TOE's baseband processor and application processor is enforced so that access to the baseband processor is strictly controlled. | |
| FPT_NOT_EXT.1 | FPT_NOT_EXT.1 supports the objective by requiring the TSF to take some action to prevent its integrity in the event of various failure conditions. | |
| FPT_NOT_EXT.2 (Objective) | FPT_NOT_EXT.2 supports the objective by requiring the TSF to make its integrity verification values available for the purpose of remote attestation. | |
| FPT_STM.1 | FPT_STM.1 supports the objective by ensuring accurate system time data is applied to audit logs. | |
| FPT_TST_EXT.1 | FPT_TST_EXT.1 supports the objective by defining the self-tests that the TSF performs to validate its own integrity. | |
| FPT_TST_EXT.2/PREKERNEL | FPT_TST_EXT.2/PREKERNEL supports the objective by requiring the TSF to verify the integrity of its bootchain prior to kernel load. | |
| FPT_TST_EXT.2/POSTKERNEL | FPT_TST_EXT.2/POSTKERNEL supports the objective by requiring the TSF to verify the integrity of stored executable code prior to its execution. | |
| FPT_TST_EXT.3 (Sel-Based) | FPT_TST_EXT.3 supports the objective by requiring the TSF to block code execution if its code signing certificate is invalid. | |
| FPT_TUD_EXT.1 | FPT_TUD_EXT.1 supports the objective by allowing users to determine the version of the TOE's hardware, software/firmware, and installed applications. | |
| FPT_TUD_EXT.2 | FPT_TUD_EXT.2 supports the objective by requiring the TSF to validate the integrity of software updates prior to installing them. | |
| FPT_TUD_EXT.3 | FPT_TUD_EXT.3 supports the objective by requiring the TSF to validate the integrity of third-party applications prior to installing them. | |
| FPT_TUD_EXT.4 (Sel-Based) | FPT_TUD_EXT.4 supports the objective by requiring the TSF to block installation of code if its associated code signing certificate is invalid. | |
| FPT_TUD_EXT.5 (Objective) | FPT_TUD_EXT.5 supports the objective by specifying the X.509 certificate that the TSF uses to verify applications prior to their installation. | |
| FPT_TUD_EXT.6 (Objective) | FPT_TUD_EXT.6 supports the objective by preventing the TSF from being rolled back to an earlier version that may have known vulnerabilities that were subsequently patched. | |
| O.PRIVACY | FDP_ACF_EXT.1 | FDP_ACF_EXT.1 supports the objective by enforcing restrictions on services that could compromise user privacy if accessed inappropriately. |
| FDP_ACF_EXT.2 (Sel-Based) | FDP_ACF_EXT.2 supports the objective by requiring the TSF to provide separate user data stores for application groups so that the privacy of that data can be maintained. | |
| FDP_BCK_EXT.1 (Objective) | FDP_BCK_EXT.1 supports the objective by allowing data to be excluded from backup operations that could compromise user privacy if disclosed. | |
| FMT_SMF_EXT.1 | FMT_SMF_EXT.1 supports the objective by requiring the TSF to implement management functions that control the extent to which user data is collected and disseminated. | |
| FMT_SMF_EXT.3 (Objective) | FMT_SMF_EXT.3 supports the objective by requiring the TSF to identify its authorized administrators so that a user knows the extent to which various administrators have access to the device. |
The Security Objectives for the TOE in sectionSection 4 Security Objectives were constructed to address threats identified in section Section 3.1 Threats. The Security Functional Requirements (SFRs) in section Section 5.1 Security Functional Requirements are a formal instantiation of the Security Objectives. The PP identifies the Security Assurance Requirements (SARs) to frame the extent to which the evaluator assesses the documentation applicable for the evaluation and performs independent testing.
This section lists the set of Security Assurance Requirements (SARs) from Part 3 of the Common Criteria for Information Technology Security Evaluation, Version 3.1, Revision 5 that are required in evaluations against this PP. Individual evaluation activities to be performed are specified in both Section 5.1 Security Functional Requirements as well as in this section.
After the ST has been approved for evaluation, the Information Technology Security Evaluation Facility (ITSEF) will obtain the TOE, supporting environmental IT, and the administrative/user guides for the TOE. The ITSEF is expected to perform actions mandated by the CEM for the ASE and ALC SARs. The ITSEF also performs the evaluation activities contained within Section 5.1 Security Functional Requirements, which are intended to be an interpretation of the other CEM assurance requirements as they apply to the specific technology instantiated in the TOE. The evaluation activities that are captured in Section 5 also provide clarification as to what the developer needs to provide to demonstrate the TOE is compliant with the PP.
Requirements As indicated in the introduction to this PP, the baseline requirements (those that must be performed by the TOE) are contained in the body of this PP. This appendix contains three other types of optional requirements that may be included in the ST, but are not required in order to conform to this PP. However, applied modules, packages and/or use cases may refine specific requirements as mandatory.
The first type () are strictly optional requirements that are independent of the TOE implementing any function. If the TOE fulfills any of these requirements or supports a certain functionality, the vendor is encouraged to include the SFRs in the ST, but are not required in order to conform to this PP.
The second type () are objective requirements that describe security functionality not yet widely available in commercial technology. The requirements are not currently mandated in the body of this PP, but will be included in the baseline requirements in future versions of this PP. Adoption by vendors is encouraged and expected as soon as possible.
The third type () are dependent on the TOE implementing a particular function. If the TOE fulfills any of these requirements, the vendor must either add the related SFR or disable the functionality for the evaluated configuration.
A subset of the User Data Protection focuses on protecting Data-At-Rest, namely FDP_DAR_EXT.1 and FDP_DAR_EXT.2. Three levels of data-at-rest protection are addressed: TSF data, Protected Data (and keys), and sensitive data. Table 6 addresses the level of protection required for each level of data-at-rest.
Table 9: : Protection of Data Levels| Data Level | Protection Required |
| TSF Data | TSF data does not require confidentiality, but does require integrity protection. (FPT_TST_EXT.2/PREKERNEL) |
| Protected Data | Protected data is encrypted while powered off. (FDP_DAR_EXT.1) |
| Sensitive Data | Sensitive data is encrypted while in the locked state, in addition to while powered off. (FDP_DAR_EXT.2) |
A subset of the User Data Protection focuses on protecting Data-At-Rest, namely FDP_DAR_EXT.1 and FDP_DAR_EXT.2. Three levels of data-at-rest protection are addressed: TSF data, Protected Data (and keys), and sensitive data. Table 6 addresses the level of protection required for each level of data-at-rest.
Table 10: : Protection of Data Levels| Data Level | Protection Required |
| TSF Data | TSF data does not require confidentiality, but does require integrity protection. (FPT_TST_EXT.2/PREKERNEL) |
| Protected Data | Protected data is encrypted while powered off. (FDP_DAR_EXT.1) |
| Sensitive Data | Sensitive data is encrypted while in the locked state, in addition to while powered off. (FDP_DAR_EXT.2) |
A subset of the User Data Protection focuses on protecting Data-At-Rest, namely FDP_DAR_EXT.1 and FDP_DAR_EXT.2. Three levels of data-at-rest protection are addressed: TSF data, Protected Data (and keys), and sensitive data. Table 6 addresses the level of protection required for each level of data-at-rest.
Table 11: : Protection of Data Levels| Data Level | Protection Required |
| TSF Data | TSF data does not require confidentiality, but does require integrity protection. (FPT_TST_EXT.2/PREKERNEL) |
| Protected Data | Protected data is encrypted while powered off. (FDP_DAR_EXT.1) |
| Sensitive Data | Sensitive data is encrypted while in the locked state, in addition to while powered off. (FDP_DAR_EXT.2) |
| Requirement | Rationale for Satisfaction |
|---|---|
| FAU_SEL.1 - Selective Audit | FAU_SEL.1 has a dependency on FMT_MTD.1 since configuration of audit data is a subset of managing TSF data. This dependency is met by the extended SFR FMT_SMF_EXT.1, which defines "configure the auditable items" as a management function and specifies the roles that may perform this, consistent with how FMT_MTD.1 would typically satisfy the dependency. |
| FCS_CKM.1 - Cryptographic Key Generation | FCS_CKM.1 has a dependency on FCS_CKM.4 for the subsequent destruction of any keys that the TSF generates. This dependency is met by the extended SFR FCS_CKM_EXT.4, which serves the same purpose. |
| FCS_CKM.1 - Cryptographic Key Generation | FCS_CKM.1 has a dependency on FCS_CKM.4 for the subsequent destruction of any keys that the TSF generates. This dependency is met by the extended SFR FCS_CKM_EXT.4, which serves the same purpose as its CC Part 2 equivalent. |
| FCS_CKM.2 - Cryptographic Key Establishment | Both iterations of FCS_CKM.2 have a dependency on FCS_CKM.4 for the subsequent destruction of any keys that the TSF establishes. This dependency is met by the extended SFR FCS_CKM_EXT.4, which serves the same purpose as its CC Part 2 equivalent. |
| FCS_COP.1 - Cryptographic Operation | All iterations of FCS_COP.1 have a dependency on FCS_CKM.4 for the subsequent destruction of any residual key material the TSF creates as part of the operation. This dependency is met by the extended SFR FCS_CKM_EXT.4, which serves the same purpose as its CC Part 2 equivalent. |
| FIA_UAU.7 - Protected Authentication Feedback | FIA_UAU.7 has a dependency on FIA_UAU.1 since protected authentication feedback is not possible without an authentication mechanism. This dependency is met by the extended SFR FIA_UAU_EXT.1, which serves the same purpose as its CC Part 2 equivalent. |
| Requirement | Action |
| FCS_STG_EXT.1.4 | Do not select "the user." |
| FMT_MOF_EXT.1.2 21 | Include in the ST. |
| FMT_MOF_EXT.1.2 25 | Include in ST. Assign personal Hotspot connections (if feature exists). |
| FMT_MOF_EXT.1.2 36 | Include in ST. |
| FMT_MOF_EXT.1.2 39 | Include in ST. Select "USB Mass storage mode." |
| FMT_MOF_EXT.1.2 41 | Include in ST. Select "USB tethering." |
| FMT_SMF_EXT.1.1 25 | Include in ST. Assign personal Hotspot connections (if feature exists). |
| FMT_SMF_EXT.1.1 36 | Include in ST. |
| FMT_SMF_EXT.1.1 39 | Include in ST. Select "USB Mass storage mode." |
| FMT_SMF_EXT.1.1 41 | Include in ST. Select both options. |
| FPT_BBD_EXT.1.1 | Include in ST. |
| FPT_TST_EXT.2.1/POSTKERNEL | Include in ST and Select "all executable code stored in mutable media." |
| FPT_TUD_EXT.5.1 | Include in ST. |
| FTA_TAB.1.1 | Include in ST. |
| Requirement | Action |
| FCS_CKM.1.1 | Select RSA with key size of 3072 or select ECC schemes. |
| FCS_CKM.2.1/UNLOCKED | Select ECC schemes, if ECC schemes are selected in FCS_CKM.1.1. |
| FCS_CKM.2.1/LOCKED | Select "RSA schemes" or select "ECC schemes that meet NIST SP 800-56A Revision 3". |
| FCS_CKM_EXT.1.1 | If "symmetric" is selected then "256 bits" must be selected. If "asymmetric" is selected and RSA scheme is selected in FCS_CKM.1.1 then "128 bits" can be selected. If "asymmetric" is selected and ECC scheme is selected in FCS_CKM.1.1, then "192 bits" can be selected. |
| FCS_CKM_EXT.2.1 | Select 256 bits. |
| FCS_CKM_EXT.3.1 | If asymmetric KEKs is selected and RSA scheme is selected in FCS_CKM.1.1 then assign 128 bits security strength. If asymmetric KEKs is selected and ECC scheme is selected in FCS_CKM.1.1 then assign 192 bits security strength. If symmetric KEKs is selected, select 256 bit security strength. |
| FCS_COP.1.1/ENCRYPT | Select 256 bits. |
| FCS_COP.1.1/HASH | Select SHA-384. |
| FCS_COP.1.1/SIGN | Assign a key size of 3072 for RSA or select ECDSA schemes. |
| FCS_COP.1.1/CONDITION | Select 256 bits. |
| FCS_RBG_EXT.1.2 | Select 256 bits. |
| FCS_TLSC_EXT.1.1 (TLS Package) | Select TLS_RSA_WITH_AES_256_GCM_SHA384 or TLS_ECDHE_ECDSA_WITH AES_256_GCM_SHA384. |
| FCS_TLSC_EXT.2.1 (TLS Package) | Select secp384r1, if included in ST (if ECC schemes are selected in FCS_CKM.1.1). |
| FDP_DAR_EXT.1.2 | Select 256 bits. |
| FIA_X509_EXT.2.2 | Select either "allow the administrator to choose..." or "not accept the certificate". |
| FMT_MOF_EXT.1.2 3 | Include in ST. |
| FMT_MOF_EXT.1.2 4 | Assign all radios on TSF. |
| FMT_MOF_EXT.1.2 5 | Assign all audio or visual collection devices on TSF. |
| FMT_MOF_EXT.1.2 19 | Include in ST. |
| FMT_MOF_EXT.1.2 21 | Include in ST. |
| FMT_MOF_EXT.1.2 44 | Include in ST. |
| FMT_MOF_EXT.1.2 45 | Include in ST (if IPsec is selected in FTP_ITC_EXT.1). |
| FMT_SMF_EXT.1.1 12 | Assign all X.509v3 certificates in the Trust Anchor Database. |
| FMT_SMF_EXT.1.1 18 | Select "f. all notifications". |
| FMT_SMF_EXT.1.1 24 | Include in ST. Assign at least USB. |
| FMT_SMF_EXT.1.1 25 | Include in ST. Assign all protocols where the TSF acts as a server. |
| FMT_SMF_EXT.1.1 36 | Include in ST. |
| FMT_SMF_EXT.2.1 | Select "wipe of protected data" and "wipe of sensitive data". |
| FAU_SAR.1.1 | Include in ST. |
| FAU_SAR.1.2 | Include in ST. |
| FAU_SEL.1.1 | Include in ST. Select "event type", "success of auditable security events", and "failure of auditable security events". |
| FCS_SRV_EXT.2.1 | Include in ST. |
| FPT_AEX_EXT.5.1 | Include in ST. |
| FPT_AEX_EXT.5.2 | Include in ST. |
| FPT_BBD_EXT.1.1 | Include in ST. |
| FTA_TAB.1.1 | Include in ST. |
| Requirement | Action |
| FMT_SMF_EXT.1.1 3 | Select "b. on a per-app basis", "c. on a per-groups of application basis" or both |
| FMT_SMF_EXT.1.1 5 | Select "b. on a per-app basis", "c. on a per-groups of application basis" or both |
| FMT_SMF_EXT.1.1 17 | Include in ST. |
| FMT_SMF_EXT.1.1 28 | Include in ST. |
| FMT_SMF_EXT.1.1 44 | Include in ST (M-M-) |
| FMT_SMF_EXT.2.1 | Select "Remove Enterprise Applications" |
| FDP_ACF_EXT.1.2 | Select "Groups of Applications" |
| FDP_ACF_EXT.2.1 | Include in ST. |
| Cipher Mode | Reference | IV Requirements |
| Electronic Codebook (ECB) | SP 800-38A | No IV |
| Counter (CTR) | SP 800-38A | "Initial Counter" shall be non-repeating. No counter value shall be repeated across multiple messages with the same secret key. |
| Cipher Block Chaining (CBC) | SP 800-38A | IVs shall be unpredictable. Repeating IVs leak information about whether the first one or more blocks are shared between two messages, so IVs should be non-repeating in such situations. |
| Output Feedback (OFB) | SP 800-38A | IVs shall be non-repeating and shall not be generated by invoking the cipher on another IV. |
| Cipher Feedback (CFB) | SP 800-38A | IVs should be non-repeating as repeating IVs leak information about the first plaintext block and about common shared prefixes in messages. |
| XEX (XOR Encrypt XOR) Tweakable Block Cipher with Ciphertext Stealing (XTS) | SP 800-38E | No IV. Tweak values shall be non-negative integers, assigned consecutively, and starting at an arbitrary non-negative integer. |
| Cipher-based Message Authentication Code (CMAC) | SP 800-38B | No IV |
| Key Wrap and Key Wrap with Padding | SP 800-38F | No IV |
| Counter with CBC-Message Authentication Code (CCM) | SP 800-38C | No IV. Nonces shall be non-repeating. |
| Galois Counter Mode (GCM) | SP 800-38D | IV shall be non-repeating. The number of invocations of GCM shall not exceed $2^{32}$ for a given secret key unless an implementation only uses 96-bit IVs (default length). |
| False Error Rate | False error rates, 90% confidence, c = 0.95 | Number of errors (rounded) | Number of test subjects needed |
| 1% (1:100) | 1% ± 0.95% | 3 | 297 |
| 0.1% (1:1000) | 0.1% ± 0.095% | 3 | 2995 |
| 0.01% (1:10000) | 0.01% ± 0.0095% | 3 | 29977 |
| 0.001% (1:100000) | 0.001% ± 0.00095% | 3 | 299797 |
| 0.0001% (1:1000000) | 0.0001% ± 0.000095% | 3 | 2997998 |
| False Error Rate | False error rates, 90% confidence, c = 0.95 | Number of errors (rounded) | Number of test subjects needed |
| 1% (1:100) | 1% ± 0.95% | 3 | 297/ND |
| 0.1% (1:1000) | 0.1% ± 0.095% | 3 | 2995/ND |
| 0.01% (1:10000) | 0.01% ± 0.0095% | 3 | 29977/ND |
| 0.001% (1:100000) | 0.001% ± 0.00095% | 3 | 299797/ND |
| 0.0001% (1:1000000) | 0.0001% ± 0.000095% | 3 | 2997998/ND |
| False Error Rate | False error rates, 90% confidence, c = 0.95 | Number of errors (rounded) | Number of test subjects needed |
| 1% (1:100) | 1% ± 0.95% | 3 | 25 |
| 0.1% (1:1000) | 0.1% ± 0.095% | 3 | 78 |
| 0.01% (1:10000) | 0.01% ± 0.0095% | 3 | 246 |
| 0.001% (1:100000) | 0.001% ± 0.00095% | 3 | 776 |
| 0.0001% (1:1000000) | 0.0001% ± 0.000095% | 3 | 2450 |
| False Error Rate | False error rates, 90% confidence, c = 0.95 | Number of errors (rounded) | Number of test subjects needed |
| 10% (1:10) | 10% ± 9.5% | 3 | 27 |
| 5% (1:20) | 5% ± 4.75% | 3 | 57 |
| 2% (1:50) | 2% ± 1.9% | 3 | 147 |
| 1% (1:100) | 1% ± 0.95% | 3 | 297 |
| Acronym | Meaning |
|---|---|
| AEAD | Authenticated Encryption with Associated Data |
| AES | Advanced Encryption Standard |
| ANSI | American National Standards Institute |
| AP | Application Processor |
| API | Application Programming Interface |
| ASLR | Address Space Layout Randomization |
| BAF | Biometric Authentication Factor |
| Base-PP | Base Protection Profile |
| BP | Baseband Processor |
| BR/EDR | (Bluetooth) Basic Rate/Enhanced Data Rate |
| BYOD | Bring Your Own Device |
| CA | Certificate Authority |
| CBC | Cipher Block Chaining |
| CC | Common Criteria |
| CCM | Counter with CBC-Message Authentication Code |
| CCMP | CCM Protocol |
| CEM | Common Evaluation Methodology |
| CMC | Certificate Management over Cryptographic Message Syntax (CMS) |
| cPP | Collaborative Protection Profile |
| CPU | Central Processing Unit |
| CRL | Certificate Revocation List |
| CSP | Critical Security Parameter |
| DAR | Data At Rest |
| DEK | Data Encryption Key |
| DEP | Data Execution Prevention |
| DH | Diffie-Hellman |
| DNS | Domain Name System |
| DSA | Digital Signature Algorithm |
| DTLS | Datagram Transport Layer Security |
| EAP | Extensible Authentication Protocol |
| EAPOL | EAP Over LAN |
| ECDH | Elliptic Curve Diffie Hellman |
| ECDSA | Elliptic Curve Digital Signature Algorithm |
| EEPROM | Electrically Erasable Programmable Read-Only Memory |
| EP | Extended Package |
| EST | Enrollment over Secure Transport |
| FAR | False Accept Rate |
| FEK | File Encryption Key |
| FFC | Finite Field Cryptography |
| FIPS | Federal Information Processing Standards |
| FM | Frequency Modulation |
| FP | Functional Package |
| FQDN | Fully Qualified Domain Name |
| FRR | False Reject Rate |
| GCM | Galois Counter Mode |
| GPS | Global Positioning System |
| GPU | Graphics Processing Unit |
| HDMI | High Definition Multimedia Interface |
| HMAC | Keyed-Hash Message Authentication Code |
| HTTPS | HyperText Transfer Protocol Secure |
| IEEE | Institute of Electrical and Electronics Engineers |
| IP | Internet Protocol |
| IPC | Inter-Process Communication |
| IPsec | Internet Protocol Security |
| KAT | Known Answer Test |
| KDF | Key Derivation Function |
| KEK | Key Encryption Key |
| LE | (Bluetooth) Low Energy |
| LTE | Long Term Evolution |
| MD | Mobile Device |
| MDM | Mobile Device Management |
| MMI | Man-Machine Interface |
| MMS | Multimedia Messaging Service |
| MMU | Memory Management Unit |
| NFC | Near Field Communication |
| NFIQ | NIST Fingerprint Image Quality |
| NIST | National Institute of Standards and Technology |
| NTP | Network Time Protocol |
| NX | Never Execute |
| OCSP | Online Certificate Status Protocol |
| OE | Operational Environment |
| OID | Object Identifier |
| OS | Operating System |
| OTA | Over the Air |
| PAD | Presentation Attack Detection |
| PAE | Port Access Entity |
| PBKDF | Password-Based Key Derivation Function |
| PD | Protected Data |
| PIV | Personal Identity Verification |
| PMK | Pairwise Master Key |
| PP | Protection Profile |
| PP-Configuration | Protection Profile Configuration |
| PP-Module | Protection Profile Module |
| PRF | Pseudorandom Function |
| PSK | Pre-Shared Key |
| PTK | Pairwise Temporal Key |
| RA | Registration Authority |
| RBG | Random Bit Generator |
| REK | Root Encryption Key |
| ROM | Read-only memory |
| RSA | Rivest Shamir Adleman Algorithm |
| SAFAR | System Authentication False Accept Rate |
| SAR | Security Assurance Requirement |
| SFR | Security Functional Requirement |
| SHA | Secure Hash Algorithm |
| SMS | Short Messaging Service |
| SoC | System On a Chip |
| SPI | Security Parameter Index |
| SSH | Secure Shell |
| SSID | Service Set Identifier |
| ST | Security Target |
| TLS | Transport Layer Security |
| TOE | Target of Evaluation |
| TSF | TOE Security Functionality |
| TSFI | TSF Interface |
| TSS | TOE Summary Specification |
| URI | Uniform Resource Identifier |
| USB | Universal Serial Bus |
| USSD | Unstructured Supplementary Service Data |
| VPN | Virtual Private Network |
| XCCDF | eXtensible Configuration Checklist Description Format |
| XTS | XEX (XOR Encrypt XOR) Tweakable Block Cipher with Ciphertext Stealing |
| Identifier | Title |
|---|---|
| [ANSI 409.1] | ANSI/CITS 409.1-2005. Biometrics Performance Testing and Reporting—Part 1: Principles and Findings." Annex B. ANSI/CITS, 2005. |
| [NFIQ 2.0] | Biometric Quality: The push towards zero error biometrics., Tabassi, Elham et al. International Biometrics Performance Conference (IBPC), 2016. Retrieved May 30, 2016. |
| [CC] | Common Criteria for Information Technology Security Evaluation -
|
| [CEM] | Common Evaluation Methodology for Information Technology Security - Evaluation Methodology, CCMB-2012-09-004, Version 3.1, Revision 5, April 2017. |
| [ISO 19989] | ISO/IEC NP 19989: Evaluation of presentation attack detection for biometrics International Organization for Standardization (ISO), 2014. |
| [BROWN] | Interval Estimation for a Binomial Proportion.Brown, Cai, and DasGupta. |
| [NFIQ 1.0] | NIST Fingerprint Image Quality and relation to PIV, Tabassi, Elham. NIST Information Technology Laboratory, 2005. Retrieved June 13, 2015. |
| [IBPC] | On security evaluation of fingerprint recognition systems-- IBPC Presentation., Henniger, Scheuermann, and Kniess.International Biometric Performance Testing Conference (IBPC), 2010. Retrieved June 12, 2015. |
| [NIST] | The NIST speaker recognition evaluation—Overview, methodology, systems, results, perspective, Doddington, Przybocki, Martin, and Reynolds. Speech Communication 31: Elsevier, 2000, Retrieved June 10, 2015. |